Bitdefender Threat Debrief | September 2023

In the modern technological landscape, organizations face both unprecedented opportunities and formidable cybersecurity risks. Daryl Plouch, one of our SOC analysts, recently wrote about the ten crucial strategies to strengthen organizational cybersecurity. Below is a summary of the insights shared:
- Internet Safety Best Practices: Emphasizing the need for cultivating basic internet safety habits among staff, the Bitdefender MDR team recommends caution regarding unfamiliar links, avoidance of untrusted software downloads, and implementing secure social media guidelines.
- Routine Phishing Campaign Tests: Phishing remains a prevalent threat. To raise awareness and enhance user knowledge, consider conducting internal phishing simulations, coupled with augmenting email protection measures.
- Approved Application List: With software vulnerabilities a concern, maintaining an application repository, housing only essential software, is advised. This not only mitigates risks but also establishes expectations for acceptable workplace applications.
- Keeping Systems Updated: Regular software updates are imperative for security. Promote timely updates, automate patch management, and employ policy compliance applications to ensure adherence.
- Admin User Privileges: Restricting administrative privileges is foundational for security. Use Group Policy settings to limit user permissions, create non-admin accounts, and segregate organization roles to minimize breach risk.
- Comprehensive Security Solutions: Emphasizing the significance of monitoring and safeguarding all endpoints, consider managed detection and response (MDR) and endpoint detection and response (EDR) solutions for enhanced defense.
- Password Requirements and Multi-factor Authentication: Weak passwords pose a significant risk. Advocate stringent password requirements, discourage password reuse, and implement multi-factor authentication (MFA) to secure logins.
- Removable Storage Devices: Due to their potential risk, consider sanitizing or prohibiting removable storage device use. Alternatives like cloud storage or policy-based restrictions can mitigate this threat.
- Backup Strategy: The importance of redundancy for disaster recovery is underscored. Options such as scheduled, remote, and cloud backups are recommended, along with regular disaster response plan testing.
- Physical Security: Good physical security complements cybersecurity efforts. Secure devices in corporate environments and use encryption to protect data at rest is highlighted.
The full article explores each strategy in detail, offering valuable insights and actionable advice to safeguard assets, maintain operations, and counter evolving cyber threats.
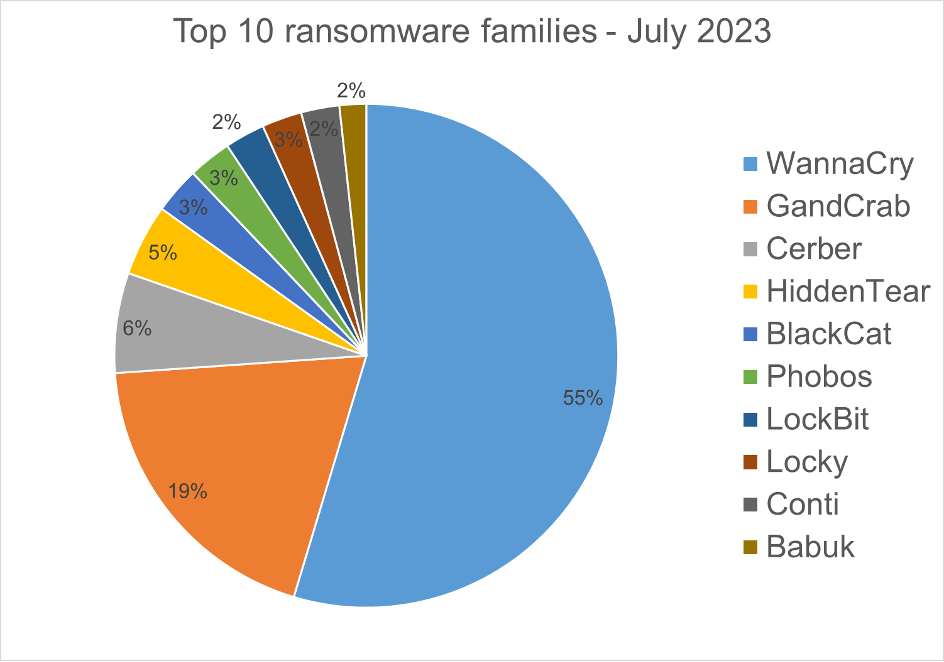
Ransomware Report
Spear phishing attacks are often used as an initial attack vector and ransomware infection is often the final stage of the kill chain. For this report, we analyzed malware detections collected in August 2023 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
Top 10 Ransomware Families
We analyzed malware detections from August 1 to August 31. In total, we identified 244 ransomware families. The number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.
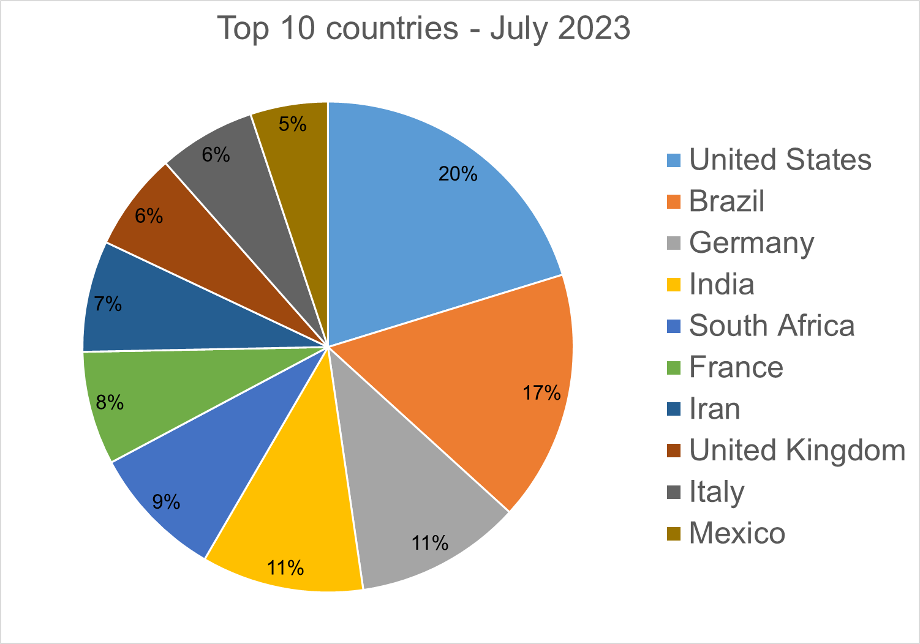
Top 10 Countries
In total, we detected ransomware from 143 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of a population is correlated to the number of detections.
Android trojans
Below are the top 10 trojans targeting Android we have seen in our telemetry during August 2023.
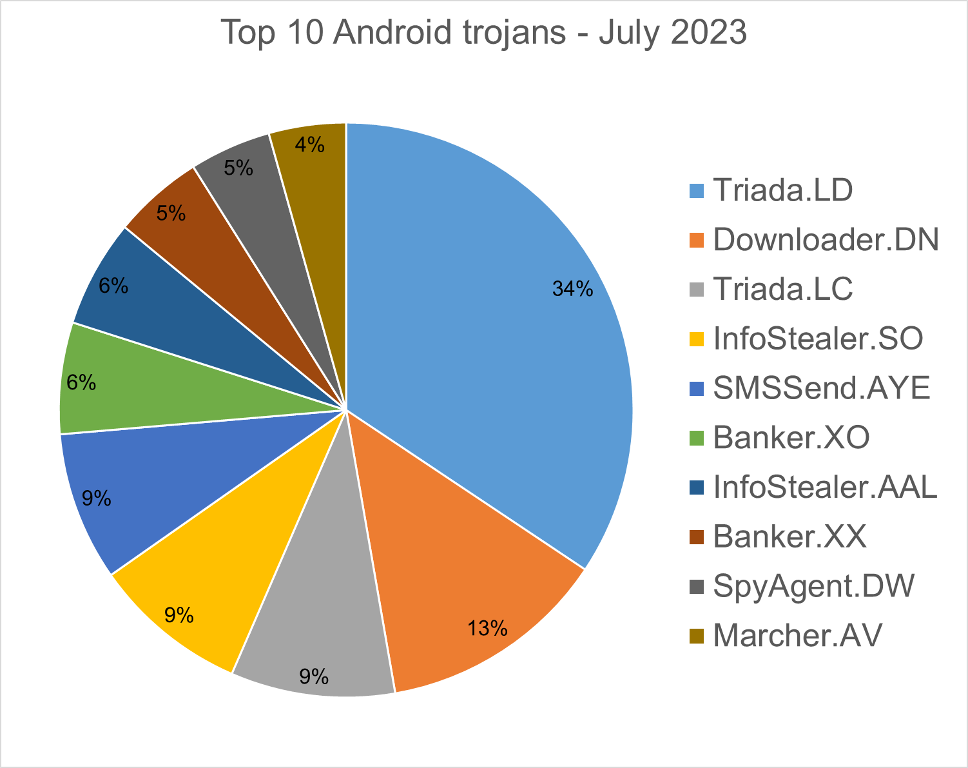
SMSSend.AYE - Malware that tries to register as the default SMS application on the first run by requesting the consent of the user. If successful, it collects the user's incoming and outgoing messages and forwards them to a Command & Control (C&C) server.
Triada.LD - Malware that gathers sensitive device info (Device IDs, Subscriber IDs, MAC addresses) and then sends it to a C&C server. The C&C server responds by sending back a link to a payload, that malware will download and execute.
Downloader.DN – Repacked applications taken from Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
InfoStealer.SO - Applications that exfiltrate users' text messages on a regular basis.
InfoStealer.AAL - Remote Administration Tool for mobile devices that allows an attacker to take control of a victim's device without needing root access. Once the malware is installed on the phone, the attacker can carry out various attacks that compromise the confidentiality and privacy of the victim's data. The tool has the ability to capture the screen content, stream live video from the phone's cameras, upload and download files from the device, and track the user's location.
Banker.AFX - Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express ...). Once installed, it locates banking applications installed on the device and tries to download a trojanized version from the C&C server.
Triada.LC – Malware that gathers sensitive information about a device (Device IDs, Subscriber IDs, MAC addresses) and sends them to a malicious C&C server. The C&C server responds by sending back a link to a payload that the malware downloads and executes.
Banker.XO - Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express ...). Once installed, it locates banking applications installed on the device and tries to download a trojanized version from the C&C server.
Marcher.AV - Applications that disguise themselves as Play Store applications. The malware tries to ask for accessibility permissions to capture keystrokes and also uses the VNC screen recording function to log the user’s activity on the phone.
SpyAgent.DW - Applications that exfiltrate sensitive data like SMS messages, call logs, contacts, or GPS location.
Homograph Phishing Report
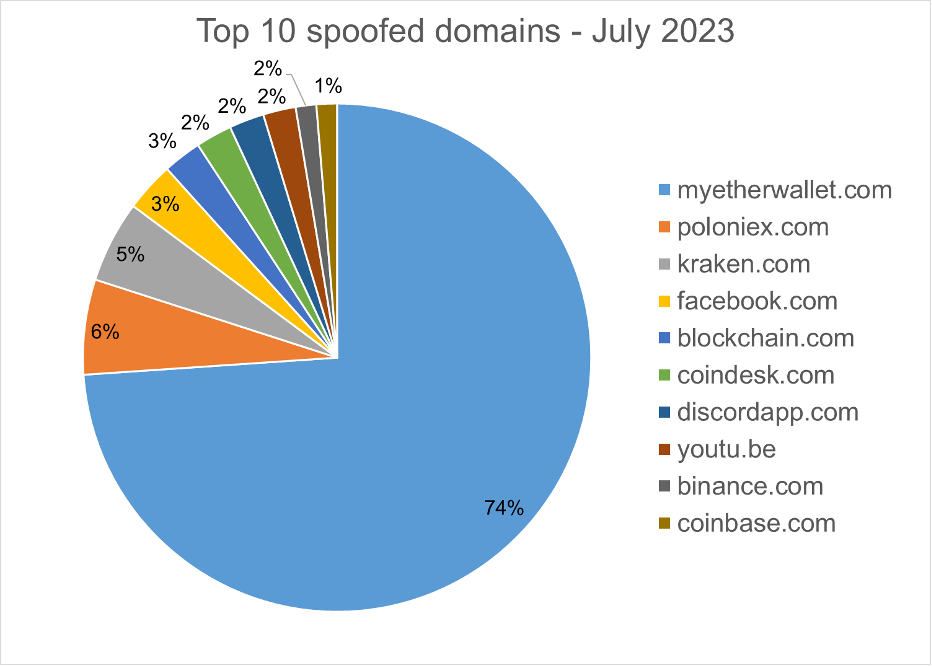
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about the “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.
About Bitdefender Threat Debrief
The Bitdefender Threat Debrief (BDTD) is a monthly series analyzing threat news, trends, and research from the previous month. Don’t miss the next BDTD release, subscribe to the Business Insights blog, and follow us on Twitter. You can find all previous debriefs here.
Bitdefender provides cybersecurity solutions and advanced threat protection to hundreds of millions of endpoints worldwide. More than 150 technology brands have licensed and added Bitdefender technology to their product or service offerings. This vast OEM ecosystem complements telemetry data already collected from our business and consumer solutions. To give you some idea of the scale, Bitdefender Labs discover 400+ new threats each minute and validate 30 billion threat queries daily. This gives us one of the industry’s most extensive real-time views of the evolving threat landscape.
We would like to thank Bitdefenders Alin Damian, Mihai Leonte, Justin Mills, Andrei Mogage, Sean Nikkel, Nikki Salas, Rares Radu, Ioan Stan, Marius Tivadar, and Horia Zegheru (sorted alphabetically) for their help with putting this report together.
tags
Author

Martin is technical solutions director at Bitdefender. He is a passionate blogger and speaker, focusing on enterprise IT for over two decades. He loves travel, lived in Europe, Middle East and now residing in Florida.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks