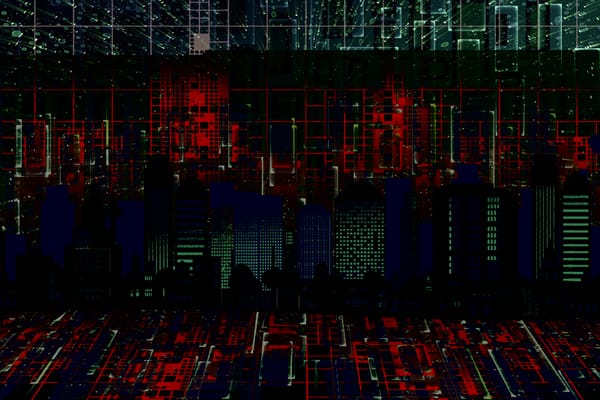
WRECKSTEEL Campaign Uses Fake HR Emails to Spy on Ukrainian Government Systems

The Computer Emergency Response Team of Ukraine (CERT-UA) has issued an alert about a sophisticated cyberattack campaign actively targeting Ukrainian government agencies and other critical infrastructure since 2024.
The attackers behind this campaign, tracked as UAC-0219, have deployed a stealer tool known as WRECKSTEEL, using phishing lures and publicly hosted scripts to steal data and screenshots from compromised computers.
Social Engineering Leads the Charge
According to CERT-UA, the attack chain starts with a well-crafted phishing email, often impersonating known agencies or HR departments. The emails reference various administrative topics—such as changes to salaries—and include a link to a file hosted on a legitimate-looking public sharing service like DropMeFiles.
The primary role of the email is to convince people it's real and relatable by using a topic that people would find interesting.
Victims who click the link are led to download a malicious file disguised as a document. Despite filenames such as "Spisok_spivrobitnykiv_na_zmenshennya_zarobitnoyi_platy_27_03_PDF.js", the file is not a PDF but a JavaScript-based VBScript loader. Once opened, the script launches a remote PowerShell payload.
Payload Steals Files, Takes Screenshots
The PowerShell script—retrieved from an attacker-controlled server (http://107[.]189[.]20[.]74/scream.ps1)—executes a series of data collection and exfiltration tasks:
- System Profiling: Gathers metadata, including IP addresses, computer names, OS versions, and disk usage.
- File Discovery: Searches user directories (e.g., Desktop, Documents) for a wide range of file extensions: *.doc, *.txt, *.pdf, *.xlsx, *.ppt, *.jpg, and more.
- Screenshot Capture: Uses PowerShell's GUI capabilities to take and store desktop screenshots silently.
- Data Exfiltration: Using curl, transferring collected files and images to the attacker's remote server.
This method allows the attackers to steal sensitive information and monitor user activity over time, making the campaign very difficult to detect.
Evolution from 2024 Techniques
CERT-UA says that earlier iterations of this attack, in 2024, used NSIS-packed executables. On the other hand, these new EXE files included:
- A PDF or JPG decoy file
- A VBScript-based stealer
- The IrfanView graphics tool (used to capture screenshots)
As of 2025, attackers have streamlined their toolkit and replaced third-party tools with native PowerShell functionality.
Threat Actor and Target Profile
The activity is attributed to the threat actor group UAC-0219. The group appears to be focused on espionage and data theft from Ukraine's public institutions and infrastructure-related entities.
CERT-UA has classified the malicious toolset used in these attacks as WRECKSTEEL, with known variants written in both VBScript and PowerShell.
tags
Author
Silviu is a seasoned writer who followed the technology world for almost two decades, covering topics ranging from software to hardware and everything in between.
View all postsRight now Top posts
How to Protect Your WhatsApp from Hackers and Scammers – 8 Key Settings and Best Practices
April 03, 2025
Outpacing Cyberthreats: Bitdefender Together with Scuderia Ferrari HP in 2025
March 12, 2025
Streamjacking Scams On YouTube Leverage CS2 Pro Player Championships to Defraud Gamers
February 20, 2025
How to Identify and Protect Yourself from Gaming Laptop Scams
February 11, 2025
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks