Settings
The firewall automatically applies a profile based on the trust level. You can have different trust levels for network connections, depending on the network architecture or the type of adapter used to establish the network connection. For example, if you have sub-networks within your company's network, you can set a trust level for each sub-network.
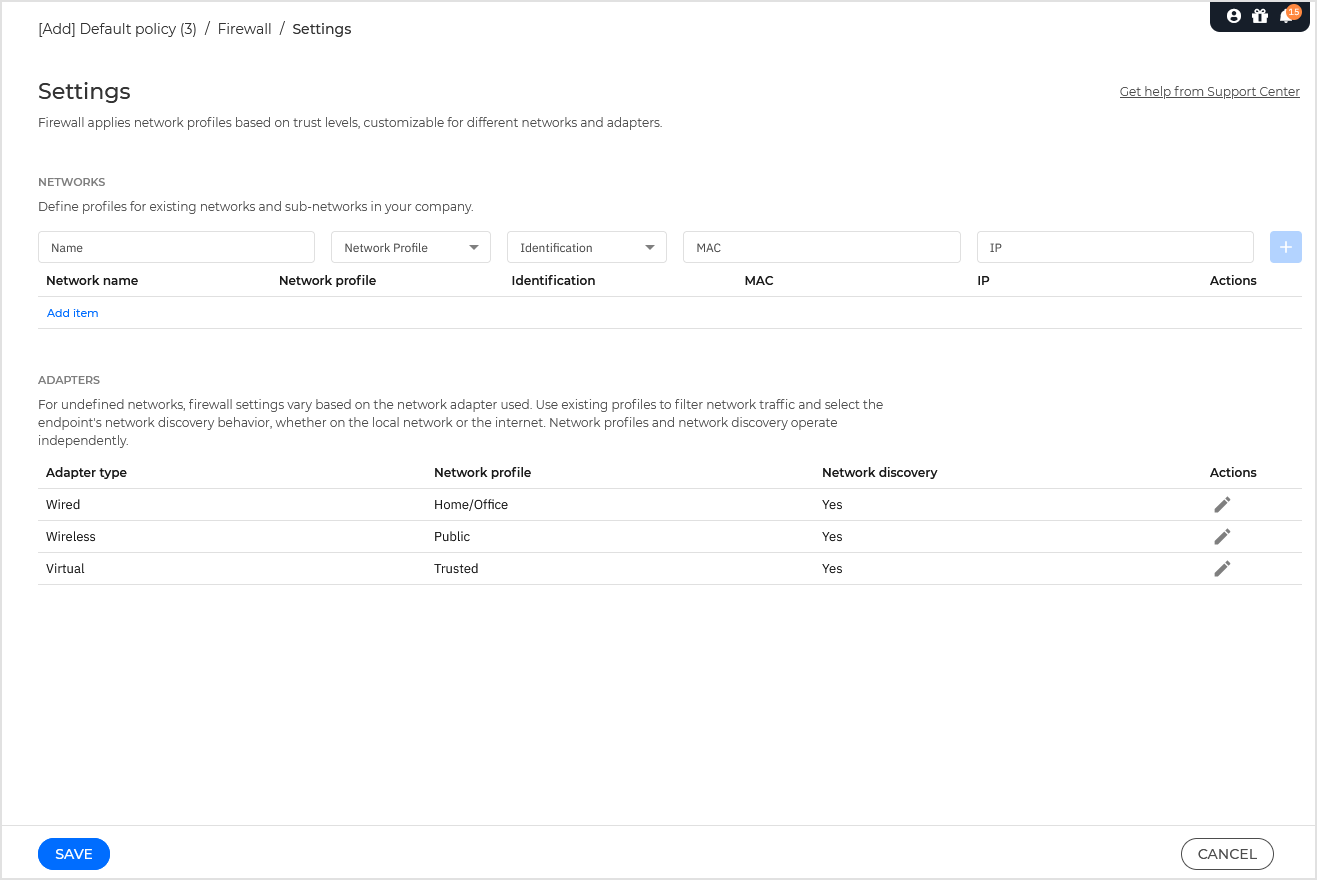
The settings are organized under the following tables:
Networks
Adapters
Networks settings
If you want the Firewall to apply different profiles to several network segments within your company, you must specify the managed networks in the Networks table. Fill in the fields from the Networks table as described herein:
Name. Enter the name by which you can recognize the network in the list.
Type. Select from the menu the profile type assigned to the network.
Bitdefender security agent automatically applies one of the four network profiles to each detected network connection on the endpoint, to define the basic traffic filtering options. The profile types are:
Trusted network. Disables the firewall for the respective adapters. The traffic is allowed and not filtered.
Home/Office network. Allows all traffic to and from computers in the local network while the other traffic is being filtered.
Public network. All traffic is filtered.
Untrusted network. Completely blocks network and Internet traffic through the respective adapters.
Identification. Select from the menu the method through which the network will be identified by the Bitdefender security agent. The networks can be identified by three methods: DNS, Gateway and Network.
DNS: identifies all endpoints using the specified DNS.
Gateway: identifies all endpoints communicating through the specified gateway.
Network: identifies all endpoints from the specified network segment, defined by its network address.
MAC. Use this field to specify the MAC address of a DNS server or of a gateway that delimits the network, depending on the selected identification method.
You must enter the MAC address in the hexadecimal format, separated by hyphens (-) or colons (:). For example, both
00-50-56-84-32-2band00:50:56:84:32:2bare valid addresses.IP. Use this field to define specific IP addresses in a network. The IP format depends on the identification method as follows:
Network. Enter the network number in the CIDR format. For example,
192.168.1.0/24, where192.168.1.0is the network address and/24is the network mask.Gateway. Enter the IP address of the gateway.
DNS. Enter the IP address of the DNS server.
After you have defined a network, click the  Add button to add it to the list.
Add button to add it to the list.
Adapters settings
If a network which is not defined in the Networks table is detected, the Bitdefender security agent detects the network adapter type and applies a corresponding profile to the connection.
The fields from the Adapters table are described as follows:
Adapter type. Displays the type of the network adapters. Bitdefender security agent can detect three predefined adapter types: Wired, Wireless and Virtual (Virtual Private Network).
Network profile. Describes the network profile assigned to a specific adapter type. The network profiles are described in the network settings section. Clicking the network type field allows you to change the setting.
If you select Let Windows decide, for any new network connection detected after the policy is applied, Bitdefender security agent applies a profile for the firewall based on the network classification in Windows, ignoring the settings from the Adapters table.
If the detection based on Windows Network Manager fails, a basic detection is attempted. A generic profile is used, where the network profile is considered Public and the stealth settings are set to On.
When the endpoint joined in Active Directory connects to the domain, the firewall profile is automatically set to Home/Office and the stealth settings are set to Remote. If the computer is not in a domain, this condition is not applicable.
Network discovery. Hides the computer from malicious software and hackers in the network or the Internet. Configure computer visibility in the network as needed, for each adapter type, by selecting one of the following options:
Yes. Anyone from the local network or the Internet can ping and detect the computer.
No. The computer is invisible from both the local network and the Internet.
Remote. The endpoint cannot be detected from the Internet. Anyone from the local network can ping and detect the endpoint.
Actions. Click the edit button to make inline changes to the network profile and network discovery.